Featured
Table of Contents
- – Vpn Tunnel - What Is It, And How Does It Work?
- – Vpn Tunnel: What Is It & Why Cyberghost Is The...
- – Intro To Networking - Virtual Private Network...
- – A Guide To Vpn Protocols
- – How A Vpn (Virtual Private Network) Works - ...
- – What Is The Secure Socket Tunneling Protocol...
- – Vpn Tunnel Types — How They Work And Best Us...
- – Guide To Vpn Protocols: Using Vpns Securely ...
- – Common Vpn And Tunneling Protocols
Vpn Tunnel - What Is It, And How Does It Work?
The strength of a tunnel depends on the type of tunneling protocol your VPN supplier uses. Some procedures are obsoleted and might not provide data encryption that is strong enough to hinder online snoops so it's a great concept for you to work with a VPN provider that counts on the strongest possible tunneling procedure.
That shuts out numerous potential users. If you're looking for the strongest security while online, you need to think about buying a VPN service supplier that counts on the Open, VPN procedure. This procedure deals with all the major operating systems, Linux, Window, and Mac, on the mobile os of Android and i, OS.
Vpn Tunnel: What Is It & Why Cyberghost Is The Best
His work has appeared in the Washington Post, Chicago Tribune, and Fox Organization. Our offerings may not cover or secure versus every type of crime, scams, or danger we write about.
The simple VPN has become progressively popular in recent years, generally because they have the capability to bypass federal government censorship and geo-blocked websites and services. Better still, a trustworthy VPN will permit you to do this without giving away who is doing the bypassing. In order for a VPN to do this, it creates what is known as a tunnel between you and the web.
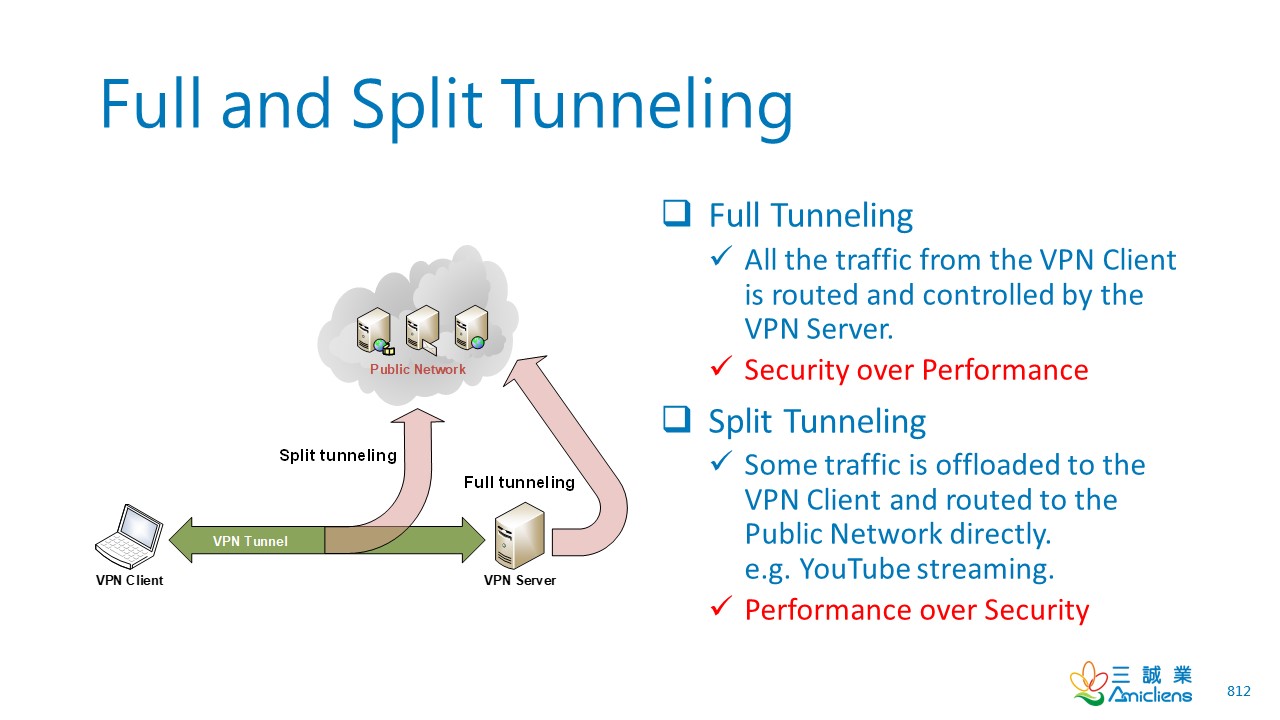
When you connect to the internet with a VPN, it produces a connection in between you and the web that surrounds your internet data like a tunnel, encrypting the data packages your device sends. While technically created by a VPN, the tunnel by itself can't be considered private unless it's accompanied with encryption strong enough to avoid federal governments or ISPs from obstructing and reading your web activity.
Intro To Networking - Virtual Private Networks & Tunneling
Let's take a better look at them.
As a Windows-based tunneling protocol, SSTP is not offered on any other os, and hasn't been individually investigated for potential backdoors constructed into the procedure. Conserving the very best for last, we have Open, VPN, a relatively recent open source tunneling protocol that utilizes AES 256-bit file encryption to secure data packages.
A Guide To Vpn Protocols
An excellent VPN service should use you the option of a minimum of these 4 kinds of tunneling protocols when going online. When it concerns the very best VPN to register for there are plenty of alternatives to select from. Obviously, if cash is tight and you're not too eager on spending anything more than you need to, trying the very best inexpensive VPN could be an alternative.
The main concern with opting for a complimentary VPN is that you typically won't get the exact same value as that supplied by a paid-for competitor. What's more, if you're using a VPN then one of the primary considerations is going to revolve around security.
How A Vpn (Virtual Private Network) Works - Howstuffworks
Free VPNs can be a little miserly when it pertains to the quantity of information you can utilize, with the running speed frequently being less outstanding than paid-for options too. If you have actually got a desire to stream video or are torrenting regularly, this may be false economy.
A low-cost VPN supplier will often have a number of the same functions and functions found in those superior editions, but you'll make some savings too.We have actually noted the very best business VPN. Tech, Radar Pro created this content as part of a paid partnership with Express, VPN. The contents of this post are entirely independent and entirely show the editorial opinion of Tech, Radar Pro.
What Is The Secure Socket Tunneling Protocol (Sstp)?
While it's tricky to set up on its own, Open, VPN is fantastic for speed, security, and encryption. Express, VPN users can toggle between UDP (optimal for speed) or TCP (ideal for connection reliability.)Among the more recent VPN protocols available to consumers, IKEv2 is thought about to be a lighter and more steady alternative than Open, VPN.
Due to its lack of file encryption and authentication features, PPTP is the fastest VPN protocol. This suggests that your web traffic can be seen by third celebrations. We do not advise using PPTP, and it is no longer supported on Express, VPN apps.
Vpn Tunnel Types — How They Work And Best Use Cases
Tabulation It's just plain creepy to think about, isn't it? The sad fact is, this is simply how your connection to the web works it's like an open window into the goings on in your home, and any nosey parker can peep through. Whether it's your Web Service Provider (ISP) wanting to track and offer your information to marketers, or deceitful hackers attempting to take your individual details to sell on the dark web, it sometimes seems like the entire world has a vested interest in snooping on your online activity.
There are a number of methods to ward off would-be online snoopers, one of which consists of using a Virtual Private Network (VPN). In a nutshell, VPNs assist you browse the web securely, independently, and without any constraints. (We've already waxed lyrical on the advantages of using a VPN in the past, so we won't harp on again excessive here).
Guide To Vpn Protocols: Using Vpns Securely In 2023
Basically, they are a series of numbers used to encrypt and decrypt information only they have access to. Hey, dropped connections take place often, even to the really best (and most expensive) VPNs. This is why most reliable VPN suppliers include a seriously useful function an automatic kill switch. Think about the kill switch as your last line of defense a digital sentinel standing constantly on guard, monitoring your connection to the server.
Tunneling uses a layered procedure model such as those of the OSI or TCP/IP protocol suite, however generally breaches the layering when using the payload to bring a service not typically supplied by the network. Normally, the shipment procedure runs at an equivalent or greater level in the layered model than the payload procedure.
Common Vpn And Tunneling Protocols

Another HTTP-based tunneling approach utilizes the HTTP CONNECT method/command. A customer problems the HTTP CONNECT command to an HTTP proxy. The proxy then makes a TCP connection to a particular server: port, and relays information between that server: port and the client connection. Because this creates a security hole, CONNECT-capable HTTP proxies frequently limit access to the CONNECT technique.
Despite the fact that the SMB protocol itself includes no file encryption, the encrypted SSH channel through which it takes a trip offers security. Local and remote port forwarding with ssh carried out on the blue computer. As soon as an SSH connection has actually been developed, the tunnel starts with SSH listening to a port on the remote or local host.
Table of Contents
- – Vpn Tunnel - What Is It, And How Does It Work?
- – Vpn Tunnel: What Is It & Why Cyberghost Is The...
- – Intro To Networking - Virtual Private Network...
- – A Guide To Vpn Protocols
- – How A Vpn (Virtual Private Network) Works - ...
- – What Is The Secure Socket Tunneling Protocol...
- – Vpn Tunnel Types — How They Work And Best Us...
- – Guide To Vpn Protocols: Using Vpns Securely ...
- – Common Vpn And Tunneling Protocols
Latest Posts
Best Vpns For Mobile In 2023
Cold War Unlock All Tool
Best Vpns For Warzone To Get Bot Lobbies In 2023
More
Latest Posts
Best Vpns For Mobile In 2023
Cold War Unlock All Tool
Best Vpns For Warzone To Get Bot Lobbies In 2023